Authorization Code flow using i2Rest bridge mode description
Overview
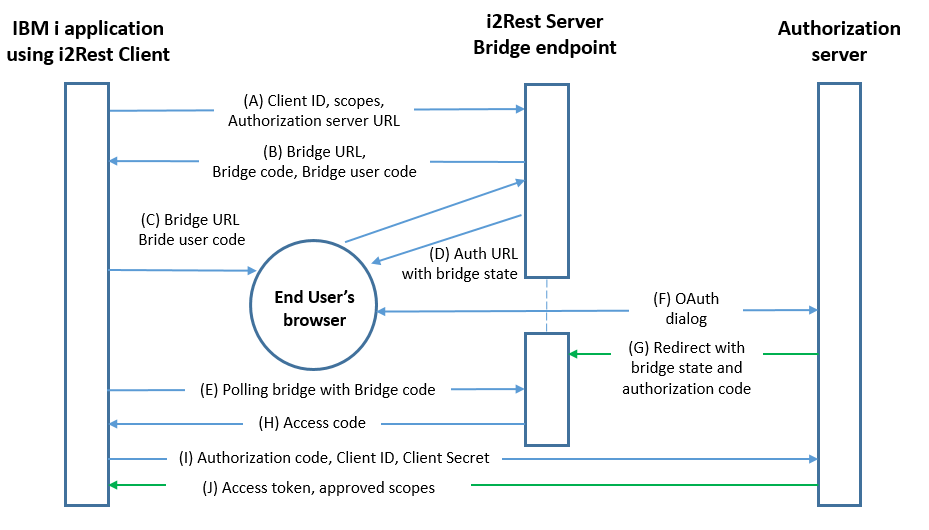
Authorization Code flow using i2Rest bridge has not too much diferencies from original Authorization Code flow - we just have to implement two "bridges" to solve IBM i functional limitations. Here are limitations and our solutions:
- i2Rest Client is not capable of interacting with the resource owner's user-agent (typically a web browser), this functions are delegated to the i2Rest Server. To perform the delegation i2Rest Client have to provide i2Rest Server with all the necessery request details and bring the end user's agent to i2Rest Server Bridge endpoint. This process is described in steps A-B-C on the scheme bellow.
- i2Rest Client also is not capable of receiving incoming requests via redirection, so I2Rest Server have to receive Authorization Server redirection with access code attached. Then obtained access code should be linked to initial I2Rest Client to Server communication, and returned to the Client uppon request. The process is described in steps G-E-H on the scheme bellow.
(А) i2Rest Client initiates the flow with a request to the I2Rest Server Bridge endpoint. The request incudes client identifier, requested scope and Authorization Server URL (authorization endpoint).
(B) I2Rest Server responds with Brigde URL, Bridge User Code and Bridge Code.
(C) i2Rest Client instructs the user to visit provided Brigde URL using device with input capability and browser support.
(D) i2Rest Server directs the resource owner's user-agent to the authorization endpoint. Request contains i2Rest Client identifier, requested scope, Bridge local state, redirection Bridge URI to which the authorization server will send the user-agent back once access is granted (or denied).
(E) i2Rest Client starts polling I2Rest Server bridge with Bridge code to determine whether the user has authorized the request.
(F) The authorization server authenticates the resource owner and performs authorization dialog to determin either access was granted or denied.
(G) The authorization server redirects the user-agent to the i2Rest Server bridge using the redirection URI provided earlier in the request or during client registration. The redirection URI includes an authorization code. Bridge local state will be checked for matching the one included in the request on step D for preventing cross-site request forgery.
(H) i2Rest Server bridge responds to Client polling request with authorization code if access was granted or with an error if access was denied.
(I) i2Rest Client requests authorization server's token endpoint with the authorization code and exchanges it for an access token. Request includes i2Rest Client credentials for authentication with the authorization server and redirection URI used to obtain the authorization code for verification.
(J) The authorization server authenticates the client, performs validation of the authorization code and the redirection URI, and, If valid, responds with an access token.
i2Rest command
Next parameters should be used to run Authorization code flow with I2Rest command.
| Parameter | Description |
|---|---|
| Authentication method | *BRIDGE must be specified |
| Command | Any of available request type can be choosen |
| API endpoint | HTTP resource to serve the request |
| User/OAuth2 client/device ID | Credentials to authenticate I2Rest Client with authorization server |
| User/OAuth2 client/dev passwd | |
| OAuth2 token endpoint | HTTP resource to be requested for an access token |
| Scope | The set of resources and operations that are allowed to application with access token |
| i2Rest access flow bridge url | Redirection URI to be passed to authorization server |
| i2Rest bridge client ID | Credentials to authenticate I2Rest Client with i2rest Server |
| i2Rest bridge client password |